Antivirus for your home network
For so many years I managed to get by without using additional antivirus software on my computer. That's basically because I'm cautious about the links that I click and I try to stay only on the beaten path of the Internet. But now, with the kids starting to venture out on the net, I found that the task of assuring that there's an antivirus on each device they are using, that it's enabled and updated, it's a tedious job to do.
That's why I began looking for a centralized solution, one that will work for everything connected to my network, and found out that on pfsense, the squid package comes with ClamAV antivirus.
ClamAV
ClamAV® is an open source (GPL) anti-virus engine used in a variety of situations including email scanning, web scanning, and endpoint security. It provides a number of utilities including a flexible and scalable multi-threaded daemon, a command line scanner and an advanced tool for automatic database updates.
Is it worthed having it as an antivirus?
Well, anything is better than nothing, right? And the ClamAV performance is not that bad as you may think, coming from a free solution. The results provided by Shadowserver in September 2019, are showing that ClamAV has a detection rate of 24%. If it doesn't seem like much, know that for example some big names as Sophos, FProt, Avast, and McAfee, have even worst results.
That being said, after downloading and activating the squid package, I have checked the Transparent HTTP Proxy setting and tested if anything was broken. But everything worked as before, it seems that the transparent part is functioning all right.
Only that it only covers the HTTP traffic. Just below, there's the SSL Man In the Middle Filtering section, that's doing the HTTPS/SSL Interception, so I checked the box and selected internal for the CA (Certificate Authority). I was quick to pat myself on the back, because a few seconds later I heard screams inside the house. "Daaaad, the Internet doesn't work!". So I broke the Internet, go figure! :)
Everyone chilled out once I left the https interception unchecked. As it seems, for this to work, I need a properly signed certificate. Not being the case for the moment, I added it to my to-do list.
Test the configuration with Eicar
Established in 1991 as the European Institute for Computer Anti-Virus Research (EICAR) we have a long track record in the fields of science, research, development, implementation and management. We represent different stakeholder groups such as Universities, recognized experts, governmental bodies and vendors who do provide neutral and independent advice – always through the lens and within the interest of the consumers. We are Independent, Distinctive and Consistent.
I got the ClamAV working, at least this is what my Services Status panel tells me, but how can I be sure? Fortunately, on the Eicar site, they are providing download links for files that will trigger your antivirus alerts. This way you know that you did a proper job and everything works as it should.
If you didn't configure the SSL Man In the Middle Filtering then only the first (HTTP) test files will trigger the alert, otherwise, they are all going to be seized by ClamAV antivirus. The SSL part is a bit more complicated, as previously noted, because it involves installing a signed certificate in pfsense. For the moment I don't have one, so I covered only the HTTP traffic. Since the first three links from Eicar are HTTP, clicking on them presented me the following message:
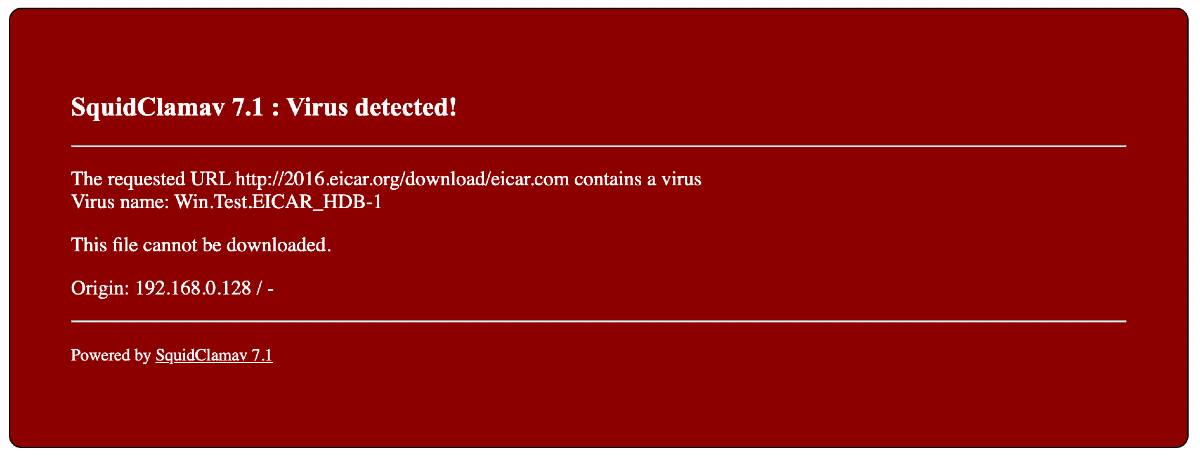
If you have SSL MITM enabled (good for you), then know that certain sites or apps don't like their certificates switched. To get them to work, just add them to the Package / Proxy Server: Access Control / ACLs whitelist, and everything will be fine.
Nothing happened when I downloaded the HTTPS files, they got through. So I need that signed certificate now.
How about performance?
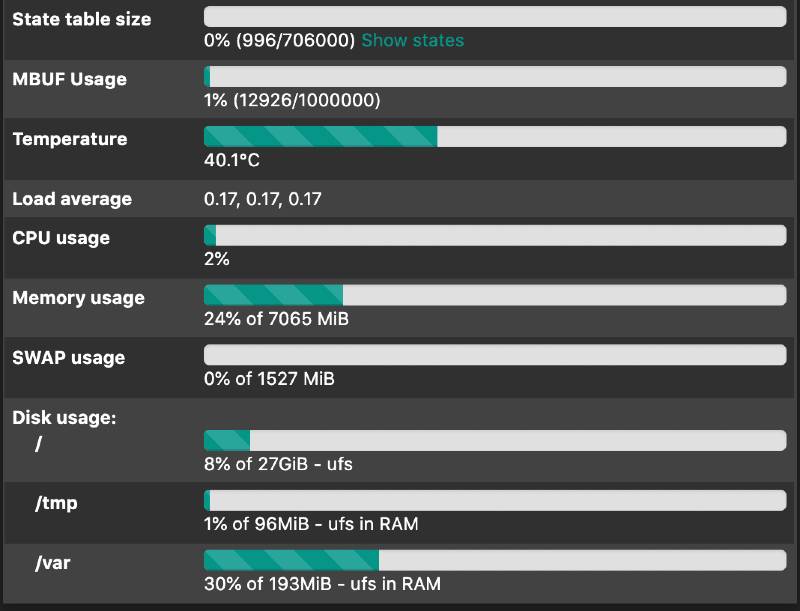
The HP T730 thin client handles it very well. I gave squid 300 MB of disk cache and 128 MB of RAM, everything else is at their default levels. In conclusion, the only thing I noticed was the bump in memory consumption, other than this nothing to report.
I do hope that with each little change in pfsense, my network becomes more secure and safe for all of us, users behind the firewall. And I will try not to break the Internet in the process.
[Update May 11, 2020]
I finally managed to get a signed certificate after installing the acme package. With this, I was then able to activate the SSL MITM and installed the certificate to all the clients (Windows, macOS, Android, and iOS devices) around the house. It worked, at least for a while, until I realized that not all the apps were functioning. The web browsing is OK, but the apps don't seem to like/use the certificate. So I finished by disabling the HTTPS/SSL Interception. And it's a shame, because today there's little to none unencrypted traffic on the web. That's a bummer, and I don't think that a solution will present itself soon...



